Understanding Address Poisoning: A Stealthy Crypto Scam Tactic
Address poisoning is a sophisticated scam that leverages transaction history to trick users into sending funds to malicious addresses. It avoids the need for private key compromise.
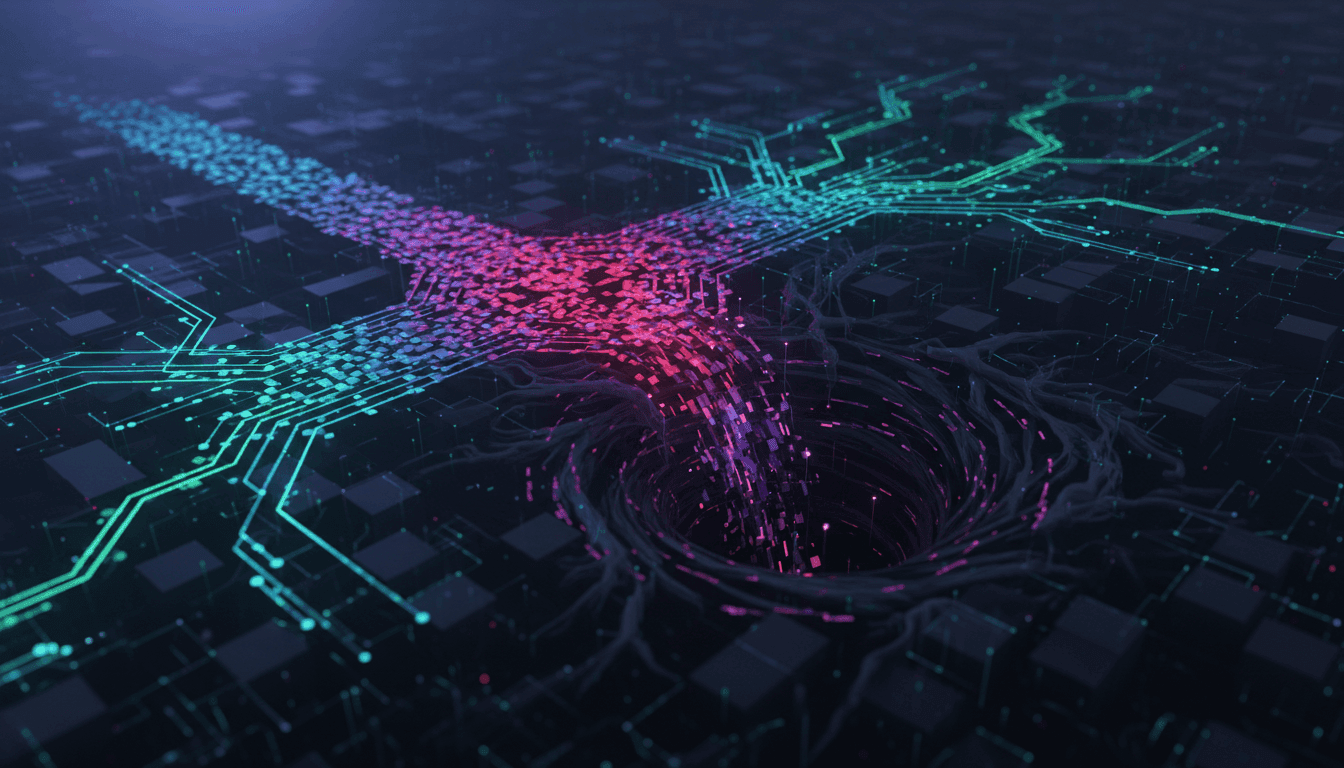
Address poisoning represents a cunning deceptive tactic within the cryptocurrency space, designed to exploit user oversight rather than directly compromise private keys. This method focuses on manipulating an individual's transaction history, creating a false sense of legitimacy around a fraudulent address.
The core mechanism of address poisoning involves introducing numerous fabricated transactions into a user's blockchain record. These fake entries are strategically designed to resemble genuine incoming or outgoing transactions, effectively muddying the waters of a wallet's activity log.
By cluttering the transaction history with these deceptive entries, scammers aim to mislead recipients. The ultimate goal is to trick the intended victim into mistakenly sending their cryptocurrency to the scammer's designated address during a future transaction, believing it to be a legitimate destination.
This technique bypasses the conventional threats associated with compromising private keys, such as phishing attacks or malware. Instead, it capitalizes on the human element of trust and the potential for error in reviewing complex transaction data, making it a subtle yet effective scam.
The continued prevalence of address poisoning highlights the importance of meticulous transaction verification for all participants in the Web3 ecosystem. Users must exercise extreme caution, cross-referencing addresses and employing best practices to avoid falling victim to such elaborate deception, underscoring the ongoing need for user education and robust security awareness.
Originally reported by CoinTelegraph.